Uncovering Hidden Weaknesses in Cryptographic Protocols
Introduction to Cryptographic Protocols
Cryptographic protocols are essential for securing digital communication. They define the rules and procedures for encrypting data, authenticating users, and ensuring privacy. However, even well-designed protocols can harbor hidden weaknesses that malicious actors might exploit.
Common Types of Vulnerabilities
Many vulnerabilities in cryptographic protocols stem from complex implementation errors or overlooked edge cases. Some common possible weaknesses include:
- Side-channel attacks that reveal secret keys through hardware analysis
- Incorrect cryptographic parameter choices that weaken encryption
- Flaws in protocol design leading to man-in-the-middle attacks
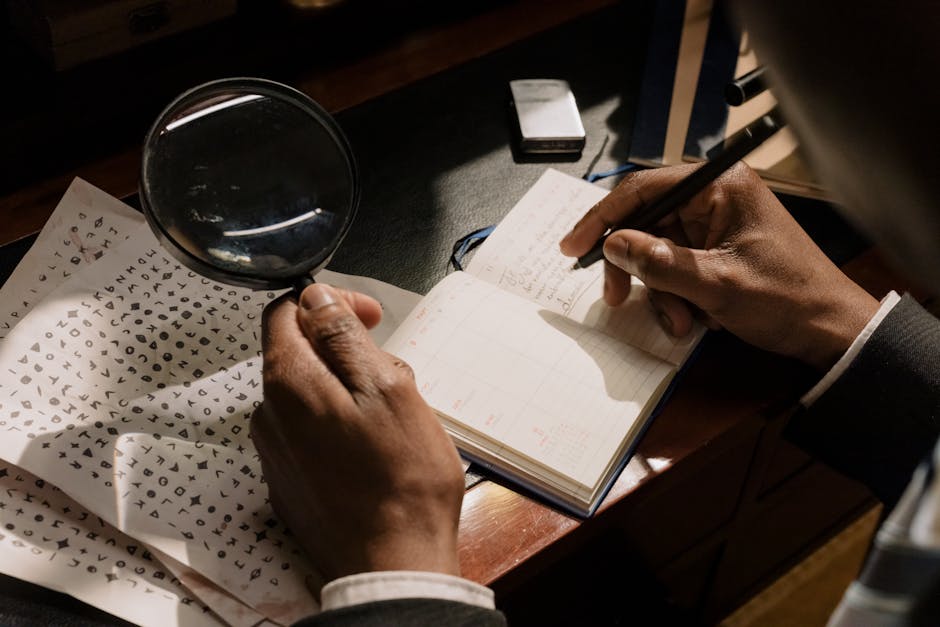
Detecting Hidden Weaknesses
Identifying hidden weaknesses requires rigorous testing and analysis. Techniques such as formal verification, cryptanalysis, and penetration testing can uncover vulnerabilities before they are exploited. It's crucial to stay updated with the latest research and tools in the field of cryptography.
Mitigating and Fixing Vulnerabilities
Once weaknesses are identified, implementing patches and updates is vital. Developers should adhere to best practices, including using well-established cryptographic libraries and protocols like TLS and PKI. Continuous review and testing help maintain the security integrity of cryptographic systems.
Conclusion
While cryptographic protocols are fundamental for secure communication, they are not immune to hidden weaknesses. Being aware of potential vulnerabilities and proactive in detection and mitigation strategies is essential for safeguarding digital information.
